- Details
-
Published: Monday, 16 January 2017 12:21
-
Written by Riccardo Gallazzi
DDoS attacks and botnets
Rakos, the new botnet that attacks Linux systems
ESET researchers published an article which explain how a botnet, called Rakos, is developing by infecting Linux servers and IoT devices through SSH attacks. The Mirai botnet, as a comparison, acts via Telnet, albeit a few attacks via SSH.
The first traces of Rakos date back to August 2016 and increased in the next months: the far is that the botnet, which is not active at the moment, is in the making and will sooner or later start DDoS attacks.
ESET researchers have understood how Rakos works: first it access to a Linux server via SSH with a brute force attack and creates folder with names such as .javaxxx, .swap, or kworker and where it works from.
Read more ...
- Details
-
Published: Wednesday, 29 June 2016 18:03
-
Written by Filippo Moriggia
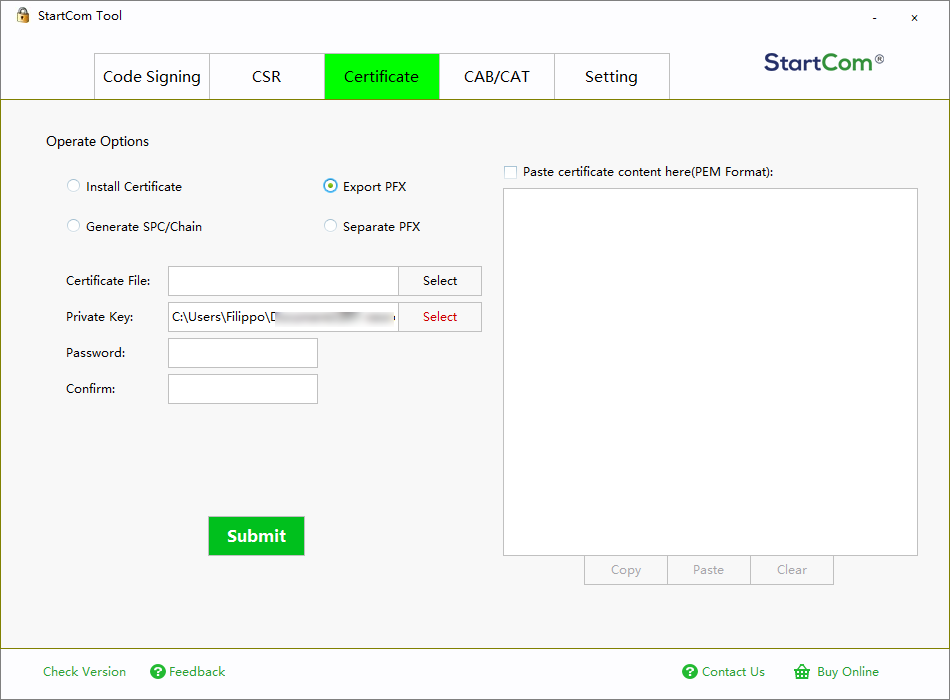
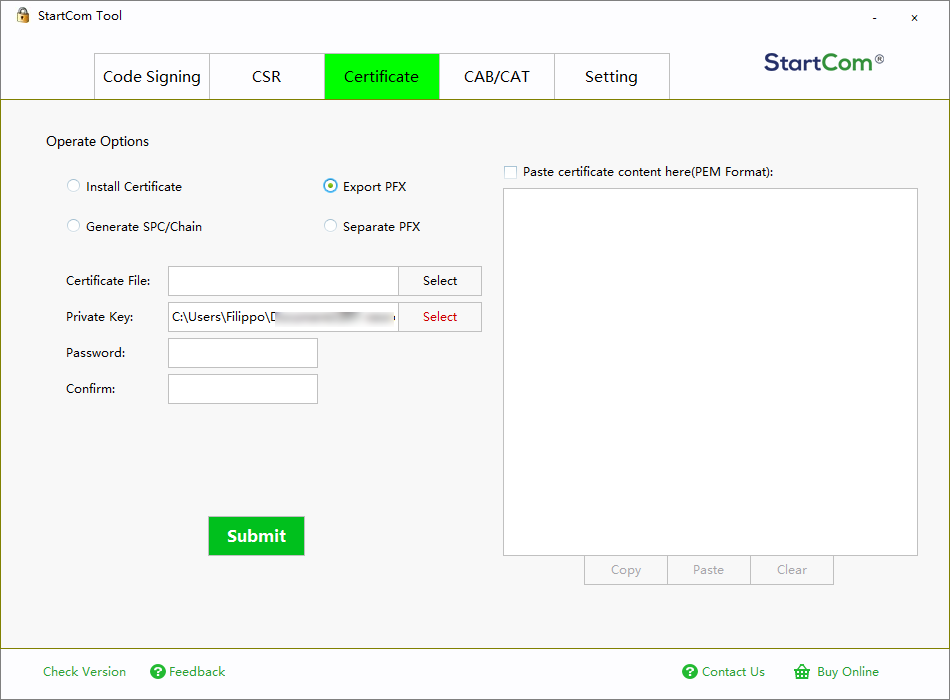
Here’s how to use SSL/TLS, S/Mime, certificates and public key cryptography in order to make Web services and email communications safer
Despite several technologies related to SSL/TLS protocols being attacked in the last 3 years, a good sysadmin or IT manager in 2016 can’t tolerate its organization still uses systems that transmit information in clear.
The use of Transport Layer Security (and its predecessor SSL) -it should be clear- it not enough to guarantee confidentiality of transmitted data on the Internet, and a quick bibliographic research shows the vast method of attacks to such protocols (like in this case and this other). TLS represents a first, fundamental security level for transmitted data, both for the access of a Web service of your company and the access to email via Webmail or IMAP/POP3/Exchange.
TLS acts as a tunnel and doesn’t modify the ongoing communication between client and server: it only adds a layer, indeed, that ciphers data between the source and the destination by using some key concepts at the basis of public key cryptography. Who has a server role needs a certificate, released by a certification authority or, in the worst case, self-signed: only who has purchased the certificate owns the private key that allows to encrypt the communication.
Read more ...
- Details
-
Published: Wednesday, 29 June 2016 17:58
-
Written by Riccardo Gallazzi
In the previous issues of GURU advisor we have dedicated article and in-depth analysis, like the one on the April 2016 issue, to the phenomenon of crypto-lockers. This plague isn’t showing any sign of slowing down and, if on one hand we have some good news (like the release of the code to decrypt data ciphered by TeslaCrypt), on the other hand new threats arise each week. For instance RAA, developed with JavaScripts and distributed via email as attached .doc file. Despite making it unharmful by disabling the Windows Script Host feature (and, subsequently, the execution of scripts), in practice RAA is another threats to your data. In this article we’d like to widen our knowledge by talking about specific tools to fight ransomware.
Prevention with backups, data protection, etc, still is the best tool at the disposal of users, of course.
A quick recap
There is a large number of tools we’ve already introduced you, so let’s recap them briefly.
- CryptoPrevent by FoolishIT sets Group Policy that prevent some ransomware from being installed.
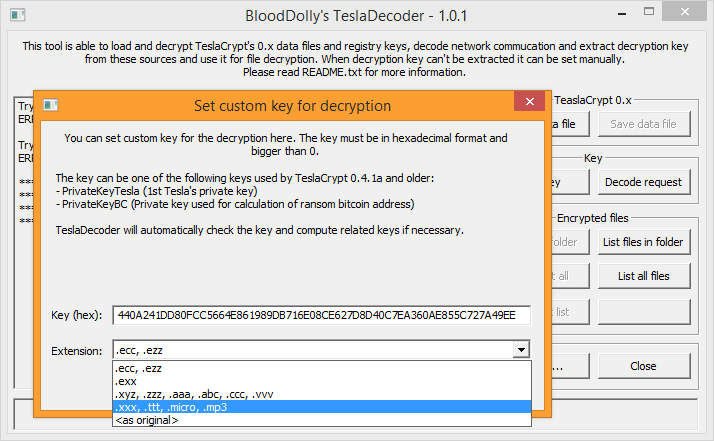
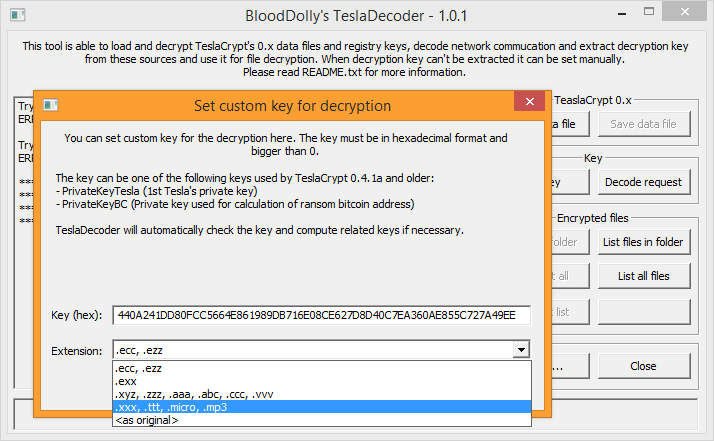
- TeslaDecoder by BloodDolly decrypts files hit by TeslaCrypt (up to version 4).
- BitDefender offers a tool against Linux Encoded (a ransomware that hits Linux systems) and a vaccine for CTB-Locker, Locky and TeslaCrypt called BD Antiransomware.
- Malwaresbytes Anti-Ransomware, formerly known as CryptoMonitor, blocks CryptoWall4, CryptoLocker, Tesla, and CTB-Locker, but it’s still in beta phase.
- Third Tier Ransomware Prevention Kit contains a set of Group Policy, filters, whitelist, settings, documents and much more to prevent infections from ransomware.
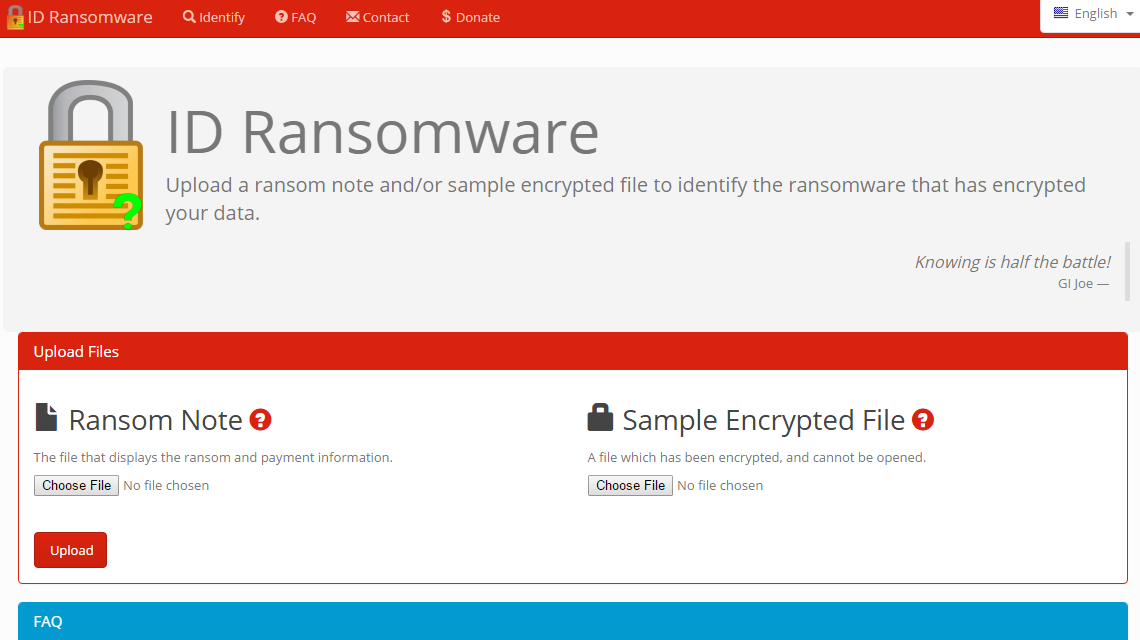
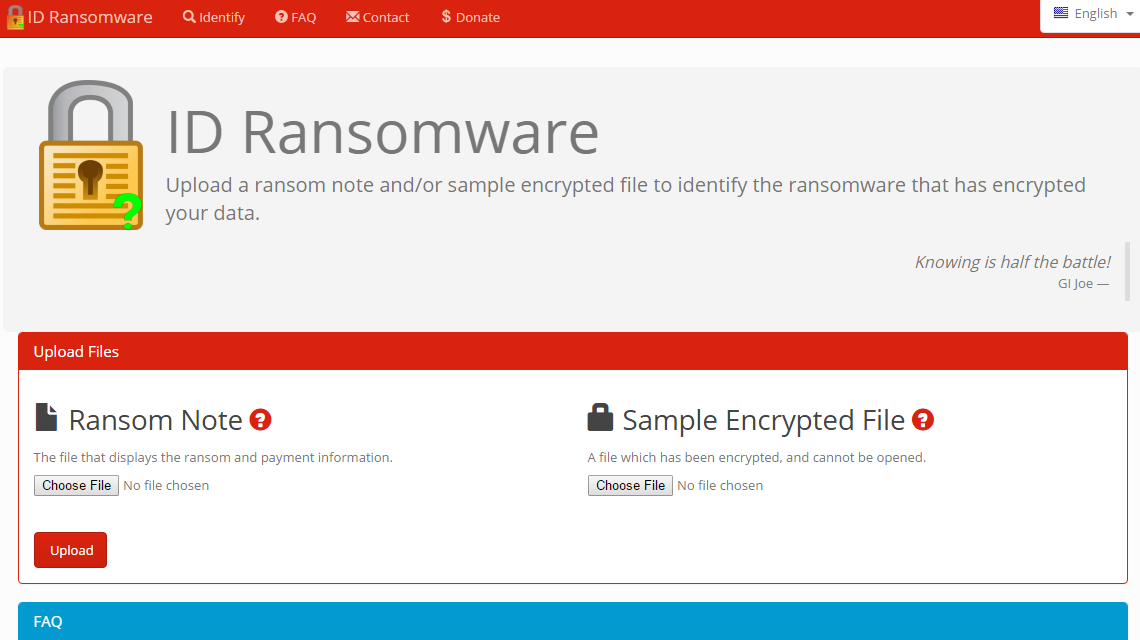
Once hit by a ransomware, the first fundamental step is to discover which crypto-ransomware is responsible for the attack. To do that, the ID Ransomware service by MalwareHunterTeam is particularly effective. By uploading an infected sample file, it identifies the type of ransomware from a pool of 103 different types available in the database. ID Ransomware doesn’t decrypt any file, it lets you know the exact nature of the ransomware attack.
Read more ...
- Details
-
Published: Wednesday, 29 June 2016 17:46
-
Written by Veronica Morlacchi
Perhaps you did underestimate them, but all virus, and in particular, the more recent Ranswomare that steal your data and ask for a ransom, are against the law. Let’s see how to behave, and let’s understand when and if filing a complaint.
As a technician, expert, IT manager or consultant you’ve maybe given advice to your colleagues, friends and clients by facing legal questions related to the IT world with a practical approach, using some common sense. Unfortunately that could not be the best way to follow, at least if you want to avoid risks, damages or consequences on your activity.
Warning: while the reflections contained in this article apply to Italian law, they may or may not apply to other laws. Each specific italian term is specified in parenthesis for a better understanding.
All malware -that is, harmful software that snake into computers and IT systems to steal information, open ports for remote control and other perils, or encrypt data with an extortion aim- clearly violate the italian juridical system and who spreads them commits a crime which is subject to sanctions according to our penal code (codice penale, c.p.). In particular, there is not only an abusive access to an IT or telematic system (ex art.615 ter c.p.), but also the diffusion of devices or programs with the specific fraud (that is, consciously) of damaging, interrupting or altering any IT or telematic system, and we can also face the criminal hypothesis of art.615 quinquies c.p.; if a “damagement of information, data and programs” is present, the crime is condemned by art.635 bis c.p. with a basic punishment of detention for 6 months to 3 years, complaint presented, with respect to art.124 c.p., within 3 months to the news of the crime (otherwise, prosecution cannot be advanced).
But things worsen if we deal with the recent threats brought by ransomware, virus that encrypt files and ask for a ransom in order to have decryption keys. In this case it’s a crime, still not specified in the IT world, of extortion, which is regulated by art.629 c.p., in accordance with the indications given by the Ministry of Justice (Ministero della Giustizia). The crime of extortion if committed by “whoever, by means of violence or threat, obliging someone to do or omit something, gains himself or others an unfair profit with damage to a third party.” From that it would derive stricter penalties to the responsibles (basic penalty is detention from 5 to 10 years and a fine from 1.000 to 4.000€), in addition the crime to being prosecutable ex officio. Moreover, it would also derive, from the transfer of money of the ransom payment, the crime of laundering (riciclaggio) ex art.648 bis c.p. in charge to who has received and “used” money.
How to behave if hit by malware or ransomware?
Read more ...
- Details
-
Published: Friday, 20 May 2016 18:32
-
Written by Lorenzo Bedin
With a coup de théâtre like in a spy movie, the developers behind the feared TeslaCrypt ransomware finally decided to end its development and diffusion project and openly published an universal key to decrypt files.
In an article on last month’s issue we dealt with the ransomware phenomenon: TeslaCrypt is for sure one of the most feared and widespread virus of this kind. Luckily, we have a good news: an universal decryption key is available and ready to be used by those who have been infected by this virus.
A researcher of Eset -the renown software house that develops the Eset antivirus- contacted the developers of TeslaCrypt with the support chat of the ransom payment portal and, pretending to be an user hit by the ransomware, asked for a decryption key. With his uttermost surprise, he was delivered with the universal alphanumeric decryption key. Naturally a proper tool is needed in order to use such key, and this problem has been solved too: the developer BloodDolly, who released months ago his TeslaDecoder tool to decrypt files hit by the first versions of TeslaCrypt (1.0 and 2.0), updated his tool so it can now decrypt files created by versions 3.0 and 4.0 of the dangerous ransomware (the ones with extensions .xxx, .ttt, .micro, .mp3 or even without any extension at all).
Read more ...
- Details
-
Published: Monday, 18 April 2016 19:44
-
Written by Filippo Moriggia
When preparing this article we’ve asked to all the main security firms to explain which technologies or tools they offer for ransomware protection. Common signature-based antiviruses are not enough to be protected as these malware are custom-tailored for every attack and the executable is masked and modified in different ways, so that it always appears as a different version.
You already know the most obvious advice: keep Windows, antivirus and all the main software (including tools like Flash, Java and Adobe Reader which are often an attack medium) up to date.
Let’s see what information we have collected from the security firms that have replied us.
Avast, mostly known for its antivirus, talked with us about DeepScreen: this technology, part of all desktop products since the 2014 version, is based on the sandbox principle. Potential malware is first executed in a sandbox to evaluate its behaviour. According to Avast, malware uses new technologies to escape from this kind of protection, but its engine is continuously updated together with definitions, so it always includes the latest control features to avoid being deceived with a clever trick.
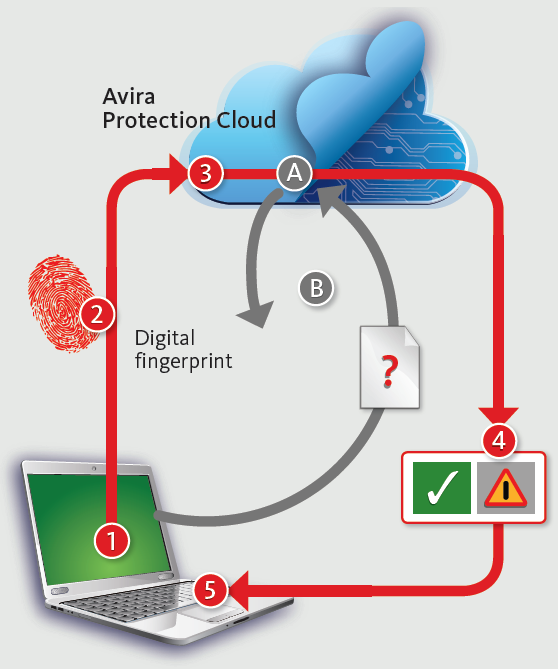
Avira recommends to activate the Cloud-based protection (Avira Protection Cloud -- see the image on the side). This technology sends a fingerprint of suspicious files to the laboratories of this famous security firms to check if it’s an already analyzed executable. If the file is not recognized it’s immediately uploaded online and analyzed. Avira leverages several techniques to overcome the anti-debugging and anti-sandboxing technologies implemented by malware.
Read more ...
- Details
-
Published: Monday, 18 April 2016 19:39
-
Written by Filippo Moriggia
How to backup PCs/servers
In order to prevent ransomware to infect your backups you can’t store them on a regular network share or on an USB disk: you must choose a local, not accessible backup or a Cloud backup like 1Backup or a similar service.
In this issue of GURU advisor we’ll explain how to leverage snapshots of the ZFS file system with FreeNAS and be protected against ransomware.
The ideal scenario is where your backup is performed on a separate Nas or server which is not linked to any domain or has reduced privileges (principle of least privileges). In any case no clients in use should directly access backups without a password (which also must not be stored). If you are already using a backup software on clients, check if you can add a pre/post backup command to use to add and the disconnect shares immediately after use.
Read more ...
- Details
-
Published: Monday, 18 April 2016 17:09
-
Written by Filippo Moriggia
Let’s return to one of the most dangerous and aggressive threats of the last years: ransomware, aka crypto-viruses: harmful software that encrypts or steals user data and asks for a ransom.
What is changing? How these viruses are evolving? Are there any reliable solution to get protected? It’s not easy to answer to all these questions, but a sysadmin, a technician or an IT manager today must know very well this topic and study all the possible strategies to protect data, be it on premises or outside the company.
Read more ...
- Details
-
Published: Monday, 14 December 2015 17:58
-
Written by Lorenzo Bedin
Here’s SecurePass, a cloud-based service for multi-platform authentication based on One Time Passwords.

Password management inside a company is always one of the most delicated and debated topics, and it gets even worse as the number of employees and services to be managed grows. GARL, a Swiss company specialized in security systems, offers SecurePass, a centralized service for identity management.
This offer is composed of four different types of subscriptions that differ in the features included and, of course, the price. The entry-level offer (Personal) is free but has a maximum number of two users and only SSO authentication; as price increases, we have the Business, Enterprise+ and Service Provider plans; the details of the number of users included and the authentication modes supported are available at this link. We’d like to point out that all the prices are quite cheap (3 or 7 € at month per user).
Read more ...
- Details
-
Published: Monday, 07 December 2015 12:29
-
Written by Filippo Moriggia
We tried the GravityZone suite available both in the cloud and on premises and ready for MSPs and resellers seeking for a complete and strong tool to keep under control the computers fleet of their clients.
The number of IT attacks is ever growing and the target in most cases are professionals and companies. The goal of these attacks has changed too: not just causing damages but also committing a scam, asking for ransoms, stealing information, passwords and money. In such a scenario an antivirus is always important even though it’s often taken for granted.

The real added value in a business environment, or for a consultant, a sysadmin or an MSP is not the simple protection with whichever engine based on signature, rather the use of a complete suite that can monitor all the client computer and servers protected, also visualizing immediately any problem and risk.
Bitdefender has gained an excellent reputation thanks in particular to a sophisticated antivirus engine, always in the first places in the tests of the most prestigious labs. Its engine is also sold to several third parties that use and resell it with different brands.
The GravityZone suite by Bitdefender is, in our opinion, still quite unknown, although it’s been for a while on the market and offers many advanced capabilities that can fulfill the needs of small and Enterprise companies. So we’ve tried it -just after the restyling that ended last month- to understand the main features and to evaluate its behaviour.
Read more ...