Kerio Control is an integrated solution for perimetral control of the network that falls in the category of UTMs (Unified Threat Management). It’s a system capable of managing threats in a unified way with a single interface for the configuration of the various settings.
Kerio Control, version 8.6.2 at the moment we write these lines, is a stateful inspection firewall, an IPS/IDS system, a traffic balancement gateway, a DHCP server, a DNS forwarder, a Web content filtering system and a VPN server for secure connections with remote users. The list of the features found in Kerio Control is long, and you might want to consult it at the official Kerio site here: http://www.kerio.com/products/kerio-control/features.
Installation
Kerio Control is available in three different formats: Hardware Appliance, Software Appliance and Virtual Appliance. The latter is the one that best fits tests and analysis because it’s available as a Virtual Hard Disk (VHD) for Microsoft Hyper-V, and as an Open Virtualization Format (OVF) for VMware ESX/ESXi, or as a prebuilt VMware Virtual Machine (VMX).
VMware Virtual Appliance
The desired image can be downloaded from the Kerio website at http://www.kerio.com/support/kerio-control. Let’s use the VMware one. Once uploaded the two .vmx and .vmdk files onto the ESXi host datastore, register the VM in the host inventory and start it. You should follow a few instructions to complete a basic configuration and then the appliance will be ready for use; in this phase of the setup it’s important to select the correct interface connected to the Internet and the one connected to the local network, which will be used for management. The administration control is available at the address https://applianceip:4081/admin.
Starting page of the management interface
MyKerio: Cloud management for MSP
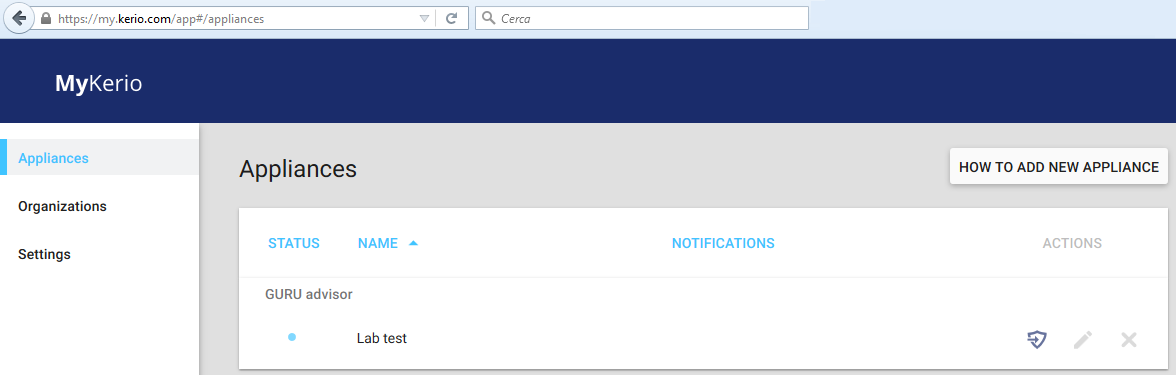
Starting with version 8.6, the Cloud service MyKerio has been introduced; MyKerio allows a centralised management of your appliance from any Internet access.
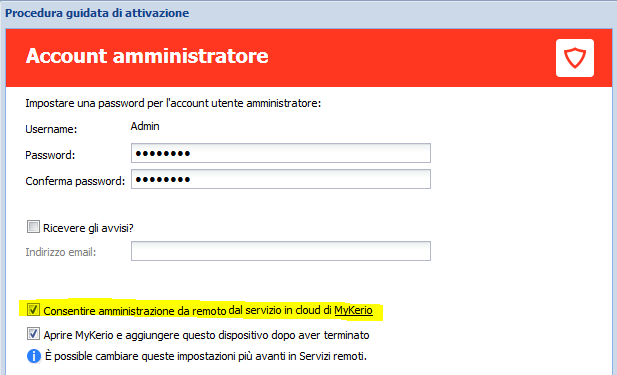
The link between the Kerio Control appliance and the cloud centralised console can be enabled during the initial setup by checking the voice “Allow remote administration from the cloud service of MyKerio”:
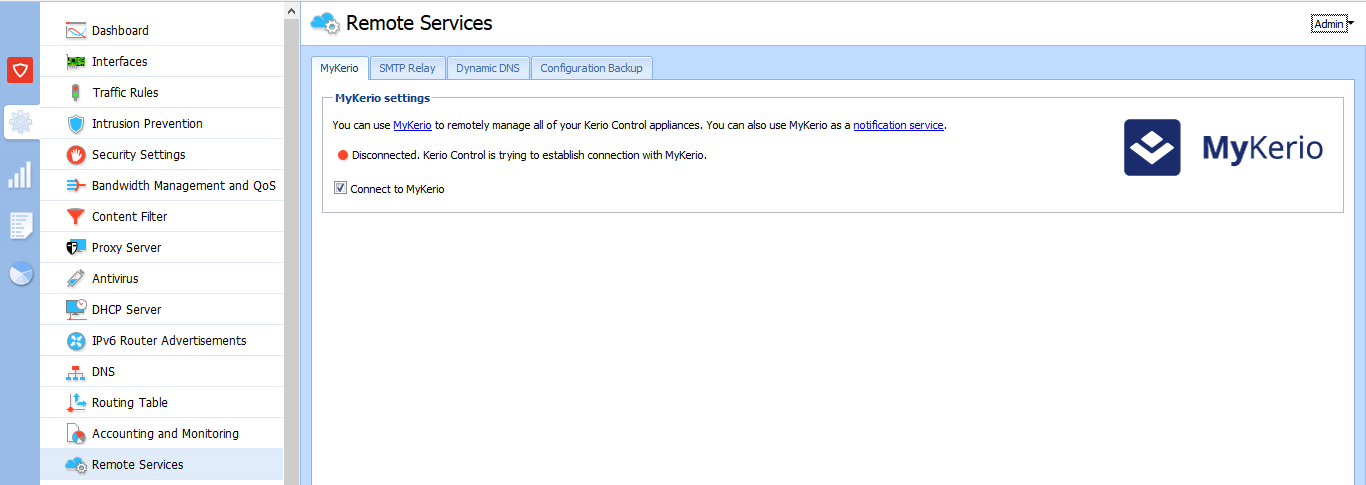
Should the service not have been activated during the initial setup, you can activate it anytime by accessing the management console and checking the flag “Connect to MyKerio” found in the Remote Service menu:
To access MyKerio cloud management service, authenticate at https://my.kerio.com/login.
Traffic rules and content filter
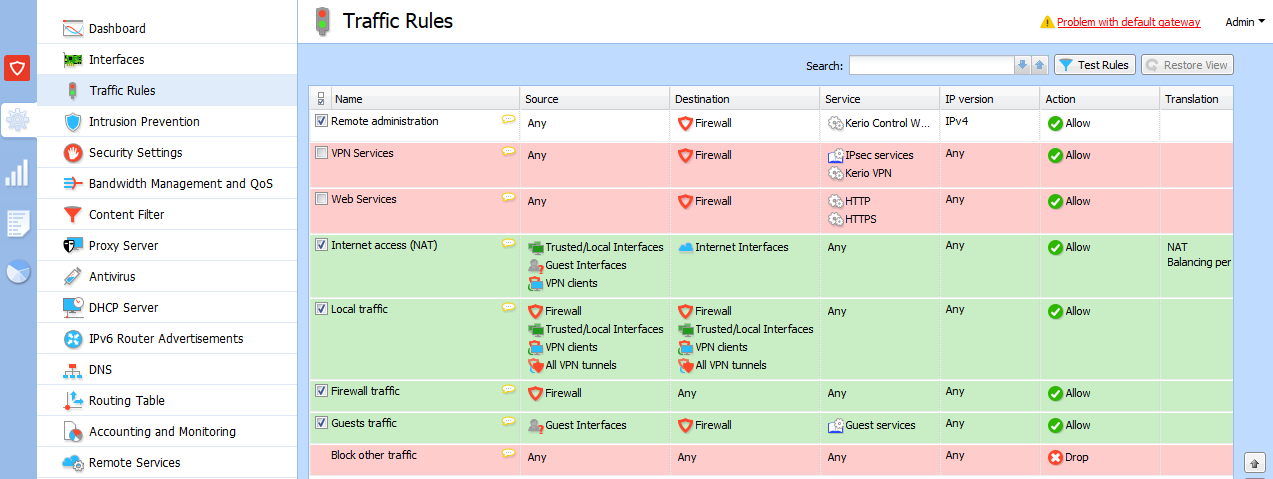
By leveraging deep packet inspection and advanced routing features, for both IPv4 and IPv6, the firewall rules section allows to protects your devices on the network; the management console has simple actions for creating and modifying rules: actions are made easier by common handy habits like right clicking on objects to access context menus, and double clicking on single field for dynamics modifications. The content filtering section is for creating policy for the control of inbound and outcoming traffic based on specific URL filters, traffic typology, content categories and time intervals.
Traffic rules settings
Content filtering settings
Filters permit to block, allow or log the access to some 141 different content categories; traffic control also limits video streaming, blocks P2P and deny the access to sites with malware contents or phishing frauds.
IPS and antivirus
The basic protection features defined with firewall rules go along with an IPS (Intrusion Prevention System) based on Snort. The service guarantees real time traffic analysis identifying potential menaces and intrusions. Traffic control is on different levels: protocol analysis, content analysis and comparison of the content with a database of rules constantly updated. As for antivirus, Kerio integrated the scansion engine of Sophos, a well-known solutions in the IT field which focuses in providing security services to organizations and companies. The AV scans the whole web traffic that goes past the appliance, including all the email attachments.
Multiple Internet Link, bandwidth management and QoS
The Multiple Internet Link feature allows to manage traffic between different Internet accesses, like an optical fibre line and and ADSL service. Accesses can configured in load-balance mode, possibly weighting each line with appropriate values, or in failover mode, that is, a line is a backup for the other.
Kerio Control performs a constant monitoring of the availability and reliability of the connections: once the Internet access is unavailable on a live, the traffic is addressed to other active lines. It’s also possible to manage each line in an independent way according to certain need, for instance a certain line can be used for a specific outgoing or incoming rule.
Balancing settings between different Internet accesses
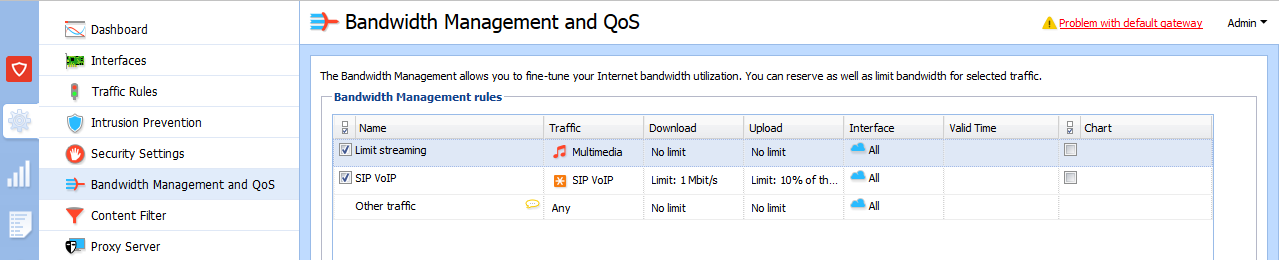
QoS services can granularly control the maximum bandwidth for each type of traffic; therefore, a maximum bandwidth can be assigned, or a certain priority can be guaranteed by setting a minimum bandwidth. The integrated limitator can preserve the available bandwidth for the most important applications. In particular, different priority levels from the general network traffic can be guaranteed for those latency-sensitive applications like VoIP or multimedia fluxes.
QoS settings
VPN and IPsec/L2TP remote access
Kerio Control integrates a VPN server capable of realising site-to-site and client-to-site connections. Configuration takes a few minimal steps; a Windows, Mac and Linux client is available for remote users. In any case, the support to the IPsec/L2TP standard is maintained in order to guarantee full compatibility with third-party softwares and solutions.
A remarkable feature is Two-Factor Authentication, the two-steps authentication that offers a second, additional level of security for remote accesses: the remote user must digit, in addition to the canonical user and password credentials, a special code -which expires after a certain amount of time- generated by an application installed on his/her own computer or mobile device. Compatible code generation apps are those compliant with RFC 6238: for instance, Google Authenticator, FreeOTP Authenticator and the Windows Phone Authenticator.
Users management: local authentication or with Active Directory
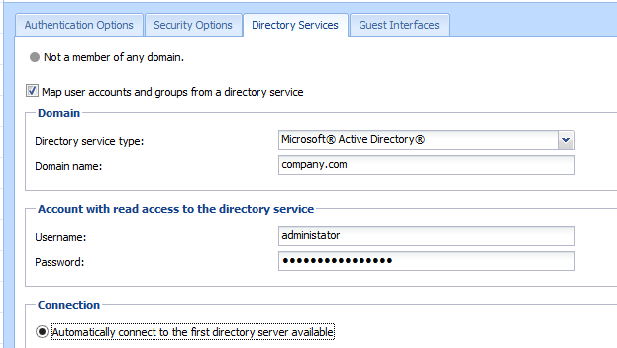
Kerio Control permits user authentication from an Active Directory or Apple Open Directory domain. Alternatively, an internal user database is available. Among the most restrictive features we find the one about allowing network access only after firewall authentication; other peculiarity: network and Web access policies can be applied to single users regardless of the device used to authenticate.
Directory services centralised authentication settings
Stats and Logs
Many times when choosing a firewall we forget to check log consultation and the possibility of verify in real time the state of the connections. These elements are managed in a good way by Kerio.
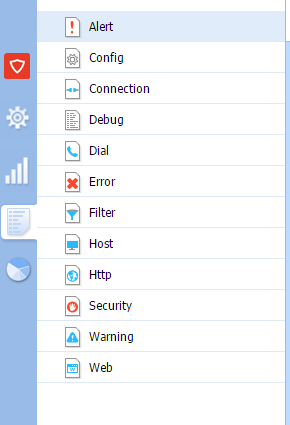
Log consulting section
The section dedicated to logs is complete and well organized; you can consult 12 different logs, and a particular emphasis is put on debug logs: you can track 73 other message types, divided into protocols, modules and services.
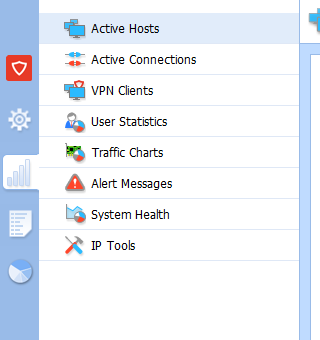
State monitoring section
Kerio also puts a lot of efforts in the section about real time state consulting of various elements, like active hosts, active connections, VPN clients, syste, state (CPU, RAM and disk) and alert messages. In the system state section the operations of reboot, firewall power-off, disk space release and upgrade can be performed; in the IP Tools menu some useful tools like Ping, Traceroute, DNS Lookup and Whois can be found as well.
Statistics
The section for reports and stats is very detailed, nonetheless easy to consult. Admins can verify with this tools the details on the activities on the Internet of each single user and monitor their behaviour: visited sited, hour of visit, terms used in researches and search engines commonly used. All these information, when cross-checked, allow to better define rules and QoS policies.
Another interesting feature is the opportunity of scheduling automatic reports at predefined hours, whose result can be sent via email.
Surely several of the features we have listed can be found in other concurrent solutions in the UTM tier; however, the thing that differentiates Kerio Control, in addition to being the declared point of strength, is the incredible ease of use.
Kerio Control is the ideal solution for those who want a product that is complete and easy to use.
New Kerio Control Box NG100
One of the first questions that arise when dealing with a commercial product is the one related to costs. Kerio Control has always been sold with licenses bases on the number of users up to today; with the release of the new Kerio Control Box NG100, a new licensing model with unlimited users has been introduced! The new Box NG100 costs 544€, a price that includes the Sophos Antivirus and Web Filtering features.
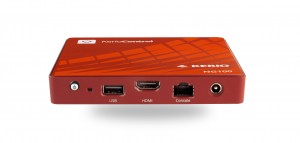

• Unlimited users
• Integrated Antivirus and Web Filtering
• 3 Gigabit Ethernet ports (LAN and WAN)
• 1 year Warranty, extendable to 3 years
Performances
• Firewall 215 Mbit/s
• IPS 98 Mbit/s
• Antivirus (32 kB files) 36 Mbit/s
• UTM (32 kB files) 30 Mbit/s
• Fanless desktop version: silent and reliable
• Dual-core Intel Bay Trail E3825 1.33 GHz processor
• Ram 4GB sodimm DDR3-1600 RAM
• Hard Disk 32GB MLC miniMSATA 3Gb/s hard disk
• Reduced dimensions: 124,26 mm x 19,4 mm x 119,66 mm
• Just 0,5kg of weight