How to protect IoT devices connected to the Internet and keep them secure
IoT is the acronym of Internet of Things, and this term defines a network where devices, sensors, objects, people and animals are equipped with a univocal ID and are capable of exchanging data through the Internet without needing a direct man-machine interaction. The idea was born from the convergence of wireless technologies and the availability of sensors and tools that are more and more small, evoluted and cheap.
This is what we wrote about IoT in our “Word of the Day” column.
On a practical side, IoT is made up by all devices connected to the Internet, and the list is very extended, as we can infer from a quick search on Shodan, the research engine for IoT devices.
A consequence of being connected to the Network is the chance of being hacked, which is not remote at all: the risk is about devices being infected and added to a botnet used for illegal stuff, like DDoS attacks, malware distribution, spam campaigns and things like these.
Credentials management
Most of non authorized accesses happens by brute-force login attempts that leverage the weakness of access data, so it’s essential to have a proper management of credentials.
First always change the default user/pwd couple with a new, complex one. This step is really important and must be done during the first installation in order to avoid forgetting to do it and leaving “zombie” devices within the internal network.
Many tools exists about creating and checking the effectiveness of a password, like this one in particular: passwords like ‘password’ or ‘12345’ are obviously not effective at all (ref. this report by Emsisoft about the worst passwords of 2016), but also passwords apparently more complex require some carefulness.
The tool we suggest to use shows the efficacy grade of the password adopted and, most important, offers hints on how to improve it.
Consider adopting a password manager, a subject we covered in this GURU article, or a centralized system like SecurePass (covered in this other GURU article).
Any default account must be disabled and then deleted. Wifi networks must use the WPA2 standard for logins, avoid using WEP.
Firewall
Every network, starting from a small home network, must be equipped and protected with a proper firewall: consumer-grade routers usually integrate this feature, but in business scenarios (but also more advanced home situations) it’s almost mandatory to use a dedicated hardware or software appliance.
The rule of thumb is to block all incoming traffic whitelisting the one to allow, while the outgoing traffic is usually permitted, however it requires a substantial pondering case per case.
Single devices too must be protected with a firewall. If the operating system is Linux, then the most immediate solution is iptables (or its front-end ufw - uncomplicated firewall), Fail2Ban is an useful solution to block non authorized login attempts: the application monitors accesses and if the login is wrong too many times (configurable), the IP the request comes from is added to the banning iptables tables, and the duration of the ban, as well as other parameters, can be set at wil.
Moreover, iptables has special tables that contain a whitelist with authorized IP addresses.
Don’t forget that all devices must be behind a NAT system, ie they must not be directly reachable from the outside and, in any case, it’s safe to limit remote connections only to essential cases.
Evaluate the adoption of a dedicated subnet or VLAN for IoT devices, which will be monitored and treated accordingly: the goal is to contain any possible infection in network segments that don’t communicate between each other.
Services and protocols
Like the firewall principle of closing ports except the ones that must remain open, for services and protocols too a similar rule applies: enable only the one explicitly required for the proper functioning of the device.
For instance telnet is an obsolete and insecure protocol that is used to gain access to a device, yet sometimes it’s enabled by default. In most cases you can safely disabled.
Use SSH instead to connect to the device, and choose an authentication system based on SSH keys (and not simple password) which guarantees a superior security level. Also disable root login.
Another caution is to change the connection port (21 by default) to another one, with a dedicated firewall rule: bear in mind that this is “security by obscurity” (security by obscurity alone is useless, but coupled with a primary security measure can bring great benefits) and changing the port can be useless as a determined hacker can use network scanners that automatically detect open ports. However it helps to reduce the number of brute-force login attempts.
A warning for all home users: disable the UPnP (Universal Plug and Play) protocol, the one that allows devices to connect on a network by communicating directly with the router and bypassing the firewall, posing a serious risk on security if enabled: all connections must go through an authentication system.
Constant updates
Newly bought devices must be updated as soon as they are installed, and a prompt and constant update policy is required: vendors release patches that fix vulnerabilities, so each device must be always up to date.
Naturally most infections leverage non updated devices which have non patched problems.
Monitoring system and asset tracking
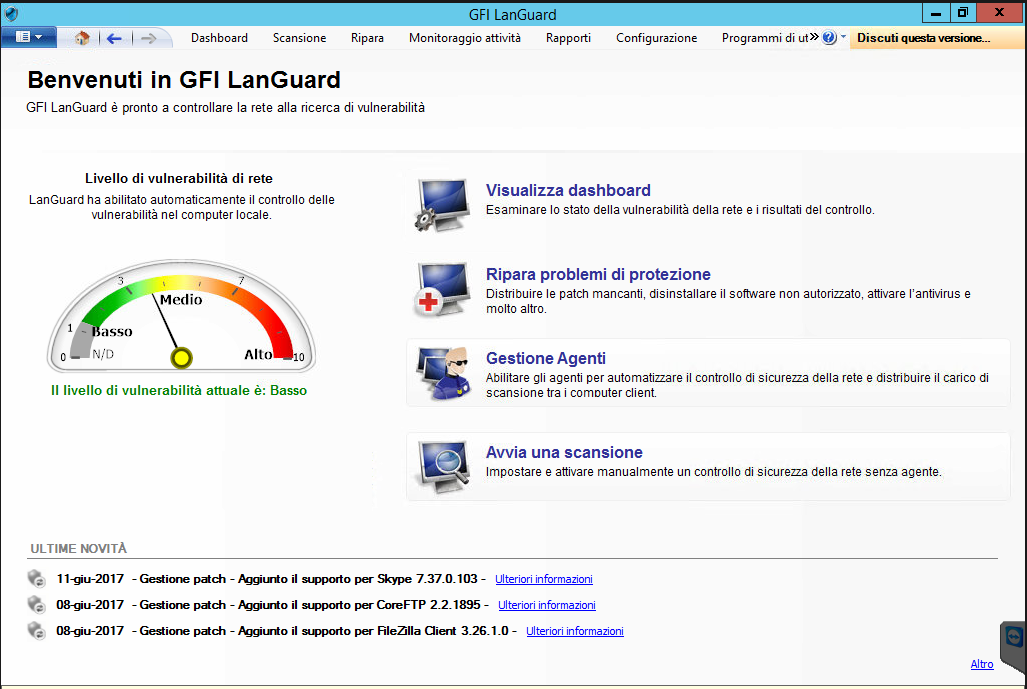
Update management is critical and weary in the case of extended installations, so it’s better to rely on an asset tracking system that tracks all devices on the network and their security status, so to avoid the risk of a single, forgotten and obsolete little IoT device that infects the whole network. If possible, choose a solution with a centralized update system in order to alleviate the burden of a manual update process and guarantee a total coverage of devices.
Then implement a monitoring system that monitors and identifies all incoming and outgoing traffic in terms of used protocols and packets size, with an appropriate alert system in case of critical situations.
We expect a growing number of network-connected devices and a growth of their adoption in pro-user habits and in generalized situations like hospitals, police stations, schools and public and private buildings; as a consequence, there will be more problem related to IoT devices security as it will become a more and more profitable market for hackers.
Producers will keep the pace with better products in terms of intrinsic security, but the starting point must be a good user education about security and the adoption of the best practices discussed in this article.