Viruses evolve along with technology, too: nowadays the goal of the hackers is exclusively to profit from IT crimes. In this scenario, ransomwares -malwares that ask for a ransom- are an explicative example of this trend.
There is no sysadmin that hasn’t already dealt, directly or not, with Cryptolocker, Cryptowall or one of their forks. These viruses quickly encrypt all the content of a computer with a secret key once it gets infected: to decypher the compromised data -when an updated backup, protected from the same virus, is not available- the only way is to pay a ransom.

Here's a screenshot you might bump into after yout files have been encrypted by a Ransomware
Actually recognised ransomwares use a strong cyphering (usually RSA-2048), and in a couple of minutes they can encrypt the whole content of the system disk, in addition to storing devices connected with USB and network shares mapped on the PC. The main target of these attacks are business companies where, unlike domestic use, the need of regaining as quickly as possible lost data is of the uttermost importance, therefore the probability of the ransom to be paid is higher. In some cases, for instance the recent Chimers, another Cryptolocker clone, to better the chances of the payment, the user is even told that private stolen data will be published on the Internet, unless the ransom is paid.
Common antivirus programs are not enough to protect from these attacks: the diffusion speed of these viruses and their attack mode makes them unsuitable.
Specific protection features have been implemented in security programs only in these last months: for instance Bitdefender with version 2016 of its suite has added an anti-ransomware feature that, unfortunately, works only on local resources of the PC. If you have been infected, paying the ransom may not be the easiest solution: it spans from 300 to thousands of euros, and the payment must be made with Bitcoin, using specific platforms like BitBoat.net that allow to buy Bitcoins with a PostePay recharge (PostePay is a stored-value card offered by the Italian mail system Poste Italiane that can be easily bought and guarantees a certain degree of anonimity). The payment itself is an outlawed act (explicitly forbidden by the norms of payment sites) and involves some risks, one of them is that the Bitcoin wallet of the criminal gets blocked, thus making necessary to use the anonymous network TOR to contact.
How to get protected
There are two main ways to protect from ransomware attacks: active protection with updated antivirus programs, firewalls and specific control softwares, and a correct backup policy.
In the former case it’s important to always check that the antivirus is properly updated: the definition database is not enough, the most recent software release must be manually installed. Almost every antivirus platform during the paid protection period allow to upgrade to the most updated release. If the antivirus of your choice doesn’t have a specific anti-ransomware protection, it may be the proper time to evaluate an alternative platform.
Ad hoc utilities
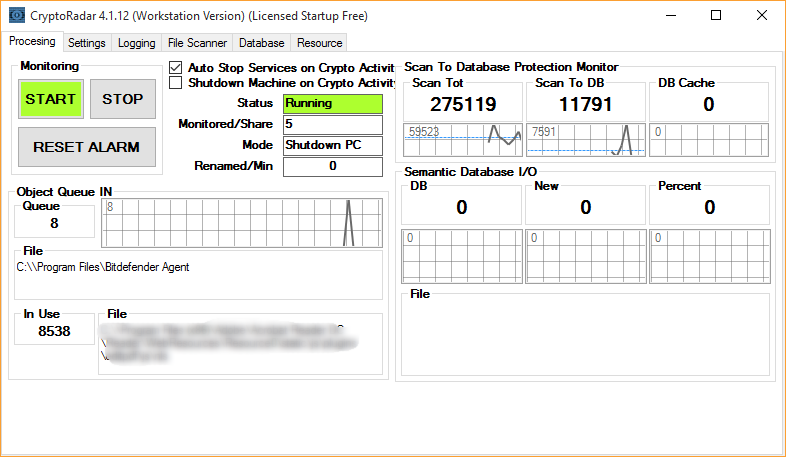
Antivirus programs can be coupled with specific software like the CryptoRadar utility that constantly monitors the state of the network shares, blocks the diffusion of the attack and, in the Client version (PC/Workstation), even shuts down the computer if the attacks is recognized. An active infection is detected as the malware performs several writing and reading operations on the disk (during the attack files are read, ciphered and individually renamed). When a system process begins to behave suspiciously, the security software blocks the execution of such processes and alerts the user.
CryptoMonitor is another interesting solution. Its operation mode includes, in addition to the monitoring operations as CryptoRadar does, also the control of specific paths of the Operative System. If suspicious activities inside these sensible areas are detected, it shuts down the computer in order to prevent the diffusion of the infection.
The usage of the count method (that is, controlling the reading/writing operations on files) in this type of prevention intrinsically leads to the detection of false positives. Bitdefender 2016, for instance, analyzes files individually and, if it’s a false positive, it permits its execution anyway.
Other companies specialized in IT security, like the English Sophos, use a different approach. Protection is based on the malware’s need to establish a connection with their control servers via Internet to let the attack begin. Both the centralized UTM (Unified Threat Management) and the single clients based Enduser solutions stop the attack by means of the analysis and the recognize of the suspicious data traffic to and from the infected device.
The best defense is Remote Backup
The best method to retrieve your own data after a ransomware attack is to have an updated backup. But backups methods must be carefully monitored and checked because Cryptolocker is capable of spreading through USB units and mapped network shares.
Softwares that performs a copy in the cloud, like 1Backup, offer a natural protection against these attacks, but, remaining in the case of the on-premises storage, NAS and SAN systems can be used as backup destinations as long as they are protected with credentials (if possible, not saved and not available to users) and not mapped on clients. Main storage products, but also ZFS-based appliances (like FreeNAS), allow to perform periodical background snapshots: these snapshots are not accessible to the user and offer a good level of protection.
The Cryptolocker phenomenon is not unnoticed to the police, and in August 2014 the operation Tovar began. FBI, together with other Policies and specialised companies (in particular, FireEye and FOX-IT) has provided ransomware attacks victims a dedicated Web site where they could upload and infected file and receive, if available, a valid decryption key. Decryptolocker.com has been closed once the agencies decide that the threat was over; surfing on the Internet you will find it often cited, however it’s no longer available.
Kaspersyk Lab’s Noransom project is more recent; developed with the collaboration of the Dutch Police at the address https://noransom.kaspersky.com, it offers a decrypting tool available for PC. This solution was made possible thanks to the addition of the Police Database which contains all the encryption keys used by cyber criminals and acknowledged after their arrest.

