- Details
-
Published: Wednesday, 26 July 2017 15:07
-
Written by Veronica Morlacchi
How a company should behave if suffering a Data Breach, according to the new General Data Protection Regulation (GDPR)? How should it do it and in which time? What are the liabilities and what sanction does it incur in if it does not behave accordingly?
We had a “Word of the Day” about Data Breaches recently, and our curiosity about the topic arose quickly on what a company should do, also from a juridical perspective, in case it is victim of an IT violation and what are its liabilities according to European Regulation 2016/679 which will become effective in a few months and it’s worth preparing for it.
Read more ...
- Details
-
Published: Wednesday, 26 July 2017 15:06
-
Written by Roberto Beneduci
Properly keeping an IT infrastructure updated is a costly and weary activity: GFI’s LanGuard is a product conceived to structure and automate management process in a complete safety.
An example how dangerous is to have non updates systems is clearly shown by the very recent wave of infections by WannaCry, the ransomware that -albeit being targeted to a restricted number of users (they could have been way more had some remedies not been found promptly)- attacked Microsoft-based infrastructures in more than 150 countries. The ransomware exploited the EternalBlue vulnerability, which is available only on non-patched version of the operating system. Yet imagine what the outcome would have been if it targeted all Windows systems.
Read more ...
- Details
-
Published: Monday, 24 July 2017 10:51
-
Written by Riccardo Gallazzi
According to W3Techs, WordPress is used in 28,1% of the existing Internet websites, and it accounts for 59% of those based on a CMS (Content Management System), and the adoption rate is ever increasing. These numbers alore are enough to understand the great diffusion of WordPress: its easy installation and customization make it suitable to several use cases, eCommerce shop included.
But such popularity brings a downside: it’s one of the most attractive platforms to hackers. Luckily damages of an hacking attack can be prevented and limited with techniques and best practices that we will discuss in this article.
Read more ...
- Details
-
Published: Monday, 24 July 2017 10:29
-
Written by Riccardo Gallazzi
How to protect IoT devices connected to the Internet and keep them secure
IoT is the acronym of Internet of Things, and this term defines a network where devices, sensors, objects, people and animals are equipped with a univocal ID and are capable of exchanging data through the Internet without needing a direct man-machine interaction. The idea was born from the convergence of wireless technologies and the availability of sensors and tools that are more and more small, evoluted and cheap.
This is what we wrote about IoT in our “Word of the Day” column.
On a practical side, IoT is made up by all devices connected to the Internet, and the list is very extended, as we can infer from a quick search on Shodan, the research engine for IoT devices.
A consequence of being connected to the Network is the chance of being hacked, which is not remote at all: the risk is about devices being infected and added to a botnet used for illegal stuff, like DDoS attacks, malware distribution, spam campaigns and things like these.
Read more ...
- Details
-
Published: Thursday, 08 June 2017 15:11
-
Written by Riccardo Gallazzi
In the middle of May we witnessed an event that could have been described as a normal ransomware attack, yet it turned out to have an incredible impact: we’re talking about WannaCry.
In a few hours, this ransomware infected thousands of computers and knocked out several infrastructures before being limited. Let’s analyze what happened and why it was an attack particular in its genre and, under certain aspects, even disturbing.
Read more ...
- Details
-
Published: Thursday, 08 June 2017 15:11
-
Written by Riccardo Gallazzi
DDoS attacks and botnets
Rakos botnet grows but remains dormant
The Rakos botnet grows but remains inactive, Morphus Labs’ Renato Marinho says.
Rakos adds 8.000 new zombie IoT each day, and continues to evolve: it now has a P2P structure. Some bots act as a (Command & Control) called Skaros, while other act as “slaves” -Checker- and launch SSH attacks to targets to add them to the botnet.
Today Rakos is composed by IoT devices as Raspberry PI (45%), OpenELEC on Raspberry PI (22%), Ubiquiti wireless access points (16%) and other.
As of now, the only remedy to the malware is to reboot the IoT device and use strong SSH credentials.
Marinho defines the botnet as “transient”: bots don’t remain as such indefinitely but only until a reboot. The force of the botnet lies in the number of bots available each day -almost 8.000- which is enough to launch an impactful DDoS attack.
Shodan launches new tool to find C&C servers
Shodan launches Malware Hunter, a tool specifically conceived to find Command and Control (C&C, sometimes C2) servers, ie servers belonging to a botnet that send commands to zombie members of the net and act as malware download center.
Malware Hunter works thanks to bots that scan the Network looking for computer configured to act as a C2 server; bots then use a predefined mode pretending to be an infected computer and communicate with the suspected C&C server: if it replies, Malware Hunter records data and makes it available with its powerful graphical tool.
Read more ...
- Details
-
Published: Monday, 10 April 2017 12:21
-
Written by Riccardo Gallazzi
DDoS attacks and botnets
Mirai botnet launches DDoS attack toward US college
At the end of March Incapsula researchers discovered a DDoS attack aimed to an UN college.
The attack lasted 54 hours and generated an average of 30.000 requests per second with a peak of 37.000 and a total of 2.8bln requests; such number can KO most devices on the network.
Less than a day after the first attack, a second one happened, but this time with a lower impact: it lasted a little bit more than an hour and a half and RPS were 15.000, on average.
The attack shows a probable new version of the Mirai botnet, as the dimensions of the attack itself and used agent users show; it had an impact on the application level rather than on the network layer.
9.793 different IP addresses (from the US, Israel, Taiwan, India, Turkey, Russia and Italy) belong to Internet of Things devices like CCTV cameras, router and DVRs; in particular, 56% of the devices belongs to a DVR model of a single manufacturer.
Read more ...
- Details
-
Published: Monday, 10 April 2017 12:21
-
Written by Riccardo Gallazzi
DDoS attacks and botnets
Linux.MulDrop14 targets Raspberry-PI devices for cryptocurrencies mining
Dr.Web researchers discovered a malware, called Linux.MulDrop14, which targets Raspberry PI devices, the popular single board computer, adding them to a botnet that mines for cryptocurrencies.
In this case devices which still have default credentials and are reachable via SSH from the outside are vulnerable: the malware installs on the device, changes the access password and adds some packages, including libraries to start mining, ZMap to scan networks for vulnerable devices and sshpass to login on any found device.
Once infected, the only way to delete the malware is reinstalling the whole operating system. Naturally default passwords must be changed.
Read more ...
- Details
-
Published: Friday, 03 February 2017 14:26
-
Written by Lorenzo Bedin
The second edition of the Security Barcamp organized by Trend Micro proves to be a very interesting meeting about IT related topics, both on a worldwide and on a more Italian-focused scale.

Rik Ferguson, Trend Micro Vice-President, was the special guest of the event and, in an extended speech, he spoke about the three main threats in the IT field of the moment and which will be in the future.
The most important threat is ransomware for sure. The phenomenon boomed in 2015 and experienced a 400% growth in terms of attack typologies and available families during the following year. The new trend is to refine and improve the attacking techniques with a particular focus on selected business targets (whose data have an important value and can justify the payment of the ransom) and social engineering, which is at the basis of these attacks.
Read more ...
- Details
-
Published: Monday, 16 January 2017 12:21
-
Written by Riccardo Gallazzi
DDoS attacks and botnets
Rakos, the new botnet that attacks Linux systems
ESET researchers published an article which explain how a botnet, called Rakos, is developing by infecting Linux servers and IoT devices through SSH attacks. The Mirai botnet, as a comparison, acts via Telnet, albeit a few attacks via SSH.
The first traces of Rakos date back to August 2016 and increased in the next months: the far is that the botnet, which is not active at the moment, is in the making and will sooner or later start DDoS attacks.
ESET researchers have understood how Rakos works: first it access to a Linux server via SSH with a brute force attack and creates folder with names such as .javaxxx, .swap, or kworker and where it works from.
Read more ...
- Details
-
Published: Wednesday, 29 June 2016 17:58
-
Written by Riccardo Gallazzi
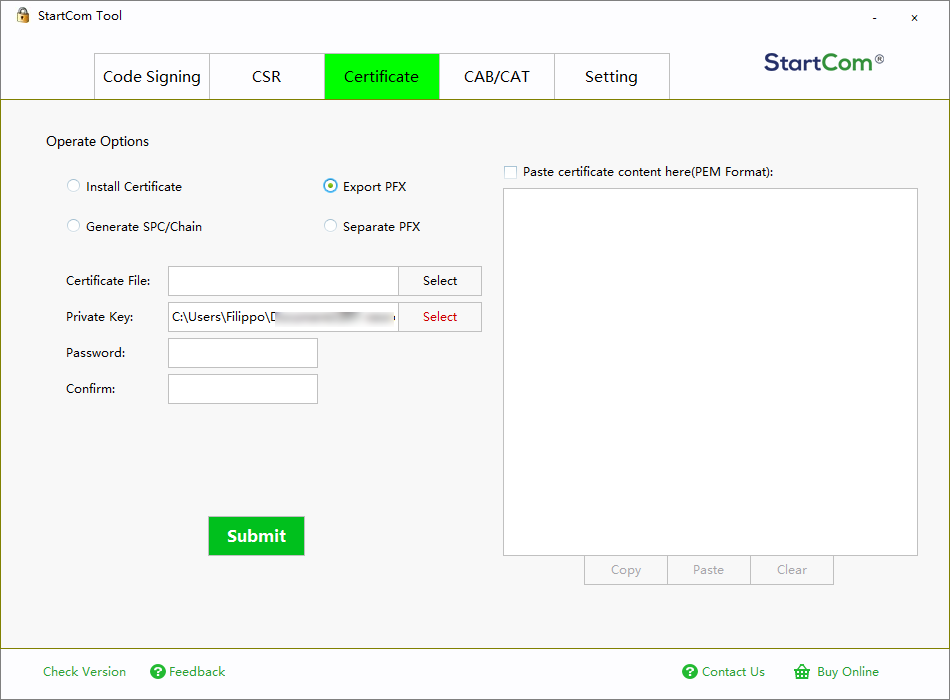
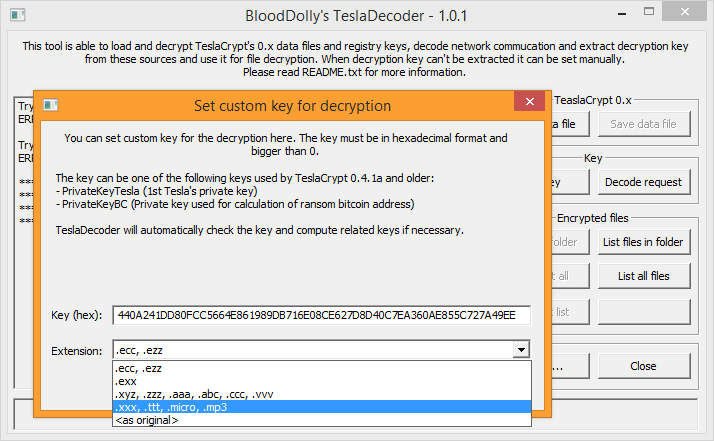
In the previous issues of GURU advisor we have dedicated article and in-depth analysis, like the one on the April 2016 issue, to the phenomenon of crypto-lockers. This plague isn’t showing any sign of slowing down and, if on one hand we have some good news (like the release of the code to decrypt data ciphered by TeslaCrypt), on the other hand new threats arise each week. For instance RAA, developed with JavaScripts and distributed via email as attached .doc file. Despite making it unharmful by disabling the Windows Script Host feature (and, subsequently, the execution of scripts), in practice RAA is another threats to your data. In this article we’d like to widen our knowledge by talking about specific tools to fight ransomware.
Prevention with backups, data protection, etc, still is the best tool at the disposal of users, of course.
A quick recap
There is a large number of tools we’ve already introduced you, so let’s recap them briefly.
- CryptoPrevent by FoolishIT sets Group Policy that prevent some ransomware from being installed.
- TeslaDecoder by BloodDolly decrypts files hit by TeslaCrypt (up to version 4).
- BitDefender offers a tool against Linux Encoded (a ransomware that hits Linux systems) and a vaccine for CTB-Locker, Locky and TeslaCrypt called BD Antiransomware.
- Malwaresbytes Anti-Ransomware, formerly known as CryptoMonitor, blocks CryptoWall4, CryptoLocker, Tesla, and CTB-Locker, but it’s still in beta phase.
- Third Tier Ransomware Prevention Kit contains a set of Group Policy, filters, whitelist, settings, documents and much more to prevent infections from ransomware.
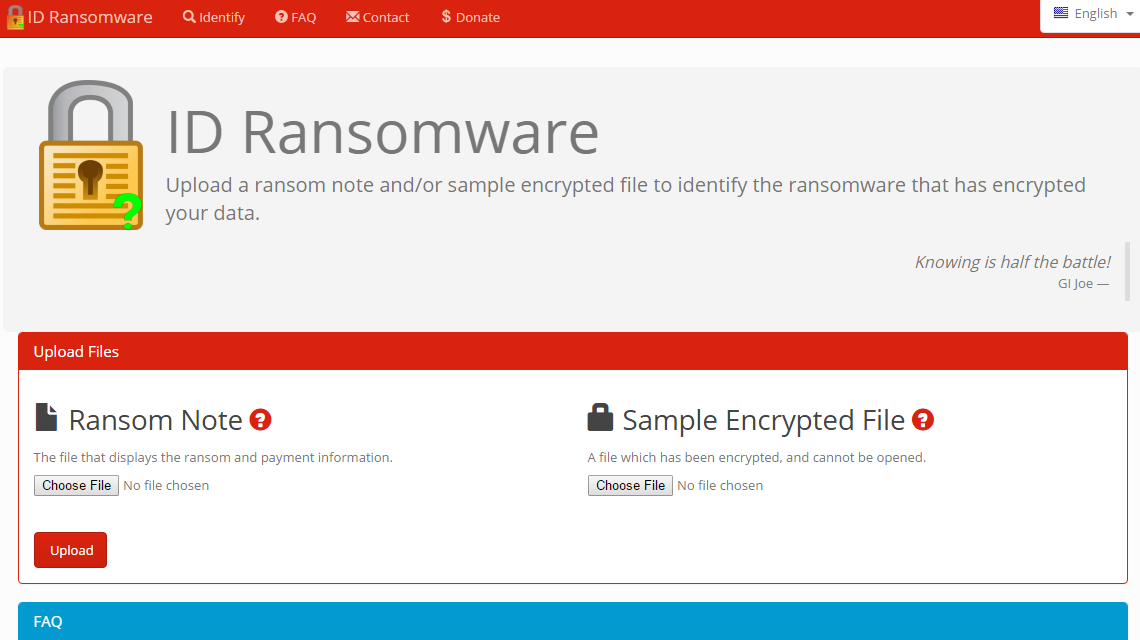
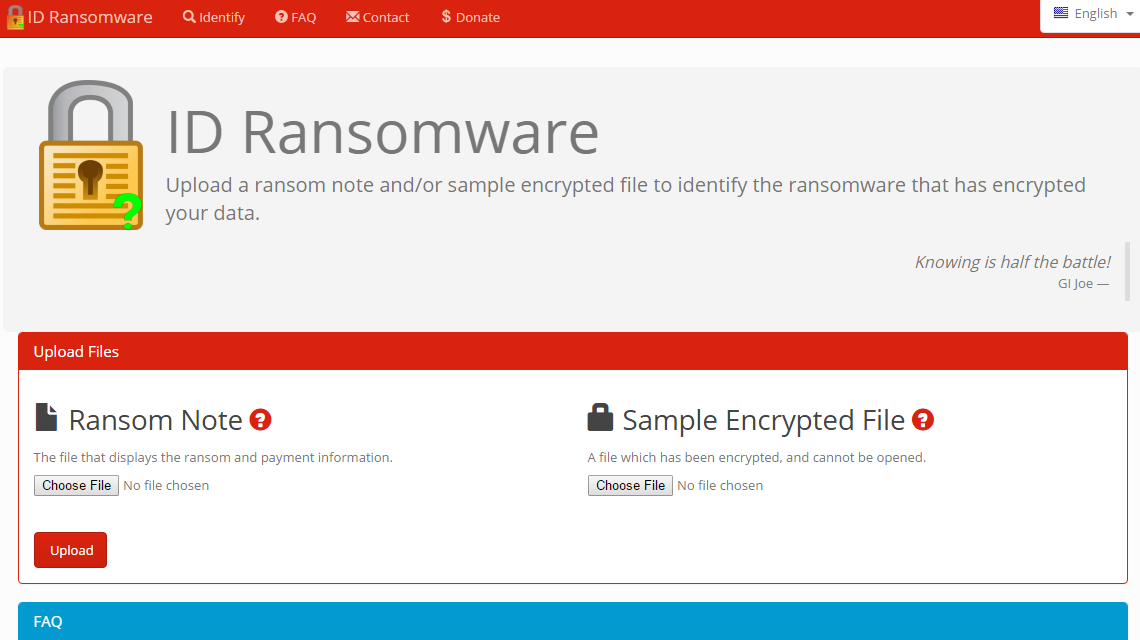
Once hit by a ransomware, the first fundamental step is to discover which crypto-ransomware is responsible for the attack. To do that, the ID Ransomware service by MalwareHunterTeam is particularly effective. By uploading an infected sample file, it identifies the type of ransomware from a pool of 103 different types available in the database. ID Ransomware doesn’t decrypt any file, it lets you know the exact nature of the ransomware attack.
Read more ...
- Details
-
Published: Wednesday, 29 June 2016 17:46
-
Written by Veronica Morlacchi
Perhaps you did underestimate them, but all virus, and in particular, the more recent Ranswomare that steal your data and ask for a ransom, are against the law. Let’s see how to behave, and let’s understand when and if filing a complaint.
As a technician, expert, IT manager or consultant you’ve maybe given advice to your colleagues, friends and clients by facing legal questions related to the IT world with a practical approach, using some common sense. Unfortunately that could not be the best way to follow, at least if you want to avoid risks, damages or consequences on your activity.
Warning: while the reflections contained in this article apply to Italian law, they may or may not apply to other laws. Each specific italian term is specified in parenthesis for a better understanding.
All malware -that is, harmful software that snake into computers and IT systems to steal information, open ports for remote control and other perils, or encrypt data with an extortion aim- clearly violate the italian juridical system and who spreads them commits a crime which is subject to sanctions according to our penal code (codice penale, c.p.). In particular, there is not only an abusive access to an IT or telematic system (ex art.615 ter c.p.), but also the diffusion of devices or programs with the specific fraud (that is, consciously) of damaging, interrupting or altering any IT or telematic system, and we can also face the criminal hypothesis of art.615 quinquies c.p.; if a “damagement of information, data and programs” is present, the crime is condemned by art.635 bis c.p. with a basic punishment of detention for 6 months to 3 years, complaint presented, with respect to art.124 c.p., within 3 months to the news of the crime (otherwise, prosecution cannot be advanced).
But things worsen if we deal with the recent threats brought by ransomware, virus that encrypt files and ask for a ransom in order to have decryption keys. In this case it’s a crime, still not specified in the IT world, of extortion, which is regulated by art.629 c.p., in accordance with the indications given by the Ministry of Justice (Ministero della Giustizia). The crime of extortion if committed by “whoever, by means of violence or threat, obliging someone to do or omit something, gains himself or others an unfair profit with damage to a third party.” From that it would derive stricter penalties to the responsibles (basic penalty is detention from 5 to 10 years and a fine from 1.000 to 4.000€), in addition the crime to being prosecutable ex officio. Moreover, it would also derive, from the transfer of money of the ransom payment, the crime of laundering (riciclaggio) ex art.648 bis c.p. in charge to who has received and “used” money.
How to behave if hit by malware or ransomware?
Read more ...