According to W3Techs, WordPress is used in 28,1% of the existing Internet websites, and it accounts for 59% of those based on a CMS (Content Management System), and the adoption rate is ever increasing. These numbers alore are enough to understand the great diffusion of WordPress: its easy installation and customization make it suitable to several use cases, eCommerce shop included.
But such popularity brings a downside: it’s one of the most attractive platforms to hackers. Luckily damages of an hacking attack can be prevented and limited with techniques and best practices that we will discuss in this article.
Reasons why to protect your WordPress site are self-evident: an hacker could access your site and steal traffic, send email spam messages, redirect your website to third-party websites, change your affiliation links, add hidden phishing pages, distribute malware and infect users with viruses. The results imply economic damages and reputation problems, in addition to being added to blacklists that are harmful to both ranking and reputation, and are hard to get out from.
Strong credentials
The topic about credentials, ie. a pair of username and password, is easier than you might think and purely relies on common sense.
One of the most used and effective way used by hackers to access a WordPress site is by brute-force attempts: an automated script picks credentials from lists of common usernames and passwords (this article by The Guardian lists ‘123456’, ‘password’ and ‘12345678’ as the most used passwords..) and tries to access by combining these couples. Therefore it’s a good start not to use common usernames as ‘admin’, ‘administrator’ or ‘webmaster’ or the likes in order to avoid giving hackers half answer to the question.
Then use complex passwords composed by at least 16 alphanumeric characters and symbols.
Take advantage of a password manager like KeePass or LastPass to create and store credentials: we have discussed about the matter in a previous article.
The same policy has to be applied to all users of the site.
Another layer of security is limiting the number of access attempts, preventing the user from logging in after a certain number of wrong attempts: this way you can limit brute-force attempts.
The easiest way to do that is to adopt a dedicated plugin.
BONUS: if possible, use a 2 factors authentication system (2FA) that adds a one-use-only code generated on the fly, perhaps with your smartphone courtesy of Google Authenticator.
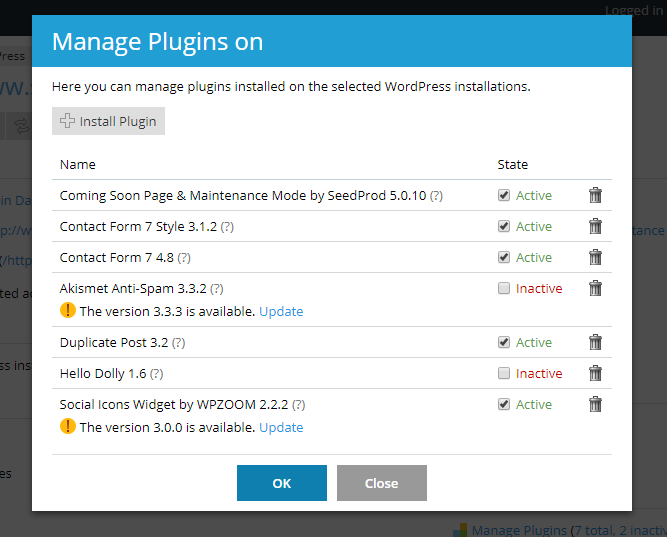
Plugins and themes management
In addition to brute-force attempts, hackers like to exploit vulnerabilities in themes, plugins and other third-party components to gain access to WordPress sites: in order to reduce the attack surface, use exclusively components that are frequently updates, have an active support and come from reliable sources.
So avoid themes download from a dubious website and then cracked: often they are a gentle way to say to hackers “please come in and hack my site”. Moreover, downloading stuff illegally might be a felony.
Avoid components that are not being developed anymore or whose support is ceased.
Rely only upon developers that offer guaranteed products and a quick support in case of problems.
WordPress has an internal directory that lists plugins and themes with user feedbacks, information about the developer and the update state.
If a component is not used anymore, uninstall it. Don’t just disable it: in this case files remain on the server and might result in an non-authorized access point.
BONUS: check periodically the WPScan Vulnerability Database, the online database with all WordPress vulnerabilities.
Frequent updates
Updates don’t only add new features or improve the ones already available, they often introduce security patches that fix problems.
WordPress has a release cycle with security releases between a major release and another that fix security issues of the CMS.
As a rule of thumb, patch often and patch early: the rule applies not only to the WordPress installation itself but also to themes, plugins and third-party components. Before upgrading, take a backup of the site, as an update might break something inside the site; if so, perform a rollback of the backup.
Updates are shown in the administration dashboard and require a few clicks -- literally!
BONUS: WordPress has a very useful automated update function that we suggest to enable. Enable automated updates of minor versions (the ones like 4.8.x) but not of major updates (like 4.x): the latter must be tested to prevent incompatibilities and assorted issues (usually there are no problems between a minor release and another).
File and folder permissions
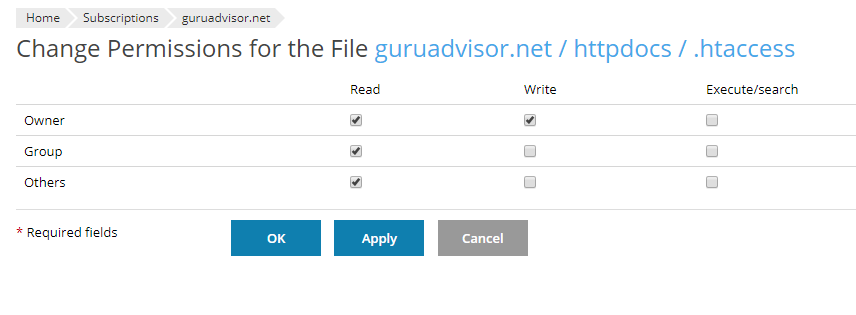
Files, folders and script need the proper system permissions (read, write, execute) in order to work as intended: insufficient permissions usually end up in a 50x error that means a server-side problem, and loose permissions allow hackers to use WordPress files as an access point to the system.
Therefore it’s mandatory to assign them with the principle of “the least permission”, that is, assign as much permissions as needed to work and nothing more.
Folders have permissions set to 755 (writeable by User, readable and executable by User, Group and Other), files to 644 (writeable by User, readable by User, Group and Other); the very important wp-config.php file has permissions set to 400 for added security. Permissions are usually assigned via FTP, by a web hosting function (if available) or by a dedicated plugin.
In no circumstance the value for files and folders should be 777 (rwx: readable, writeable and executable by User, Group and Other), save for troubleshooting situations.
BONUS: delete the readme.html file (located in the website root) which contains system information that could be exploited by a hacker. As each WordPress update regenerates the file, you have to delete it manually after every system update.
Monitoring and alerts
Unfortunately sometimes your best isn’t enough and sites get hacked despite your efforts.
In some cases the damage is clear, for instance the homepage is changed with a “You’ve been hacked!!!” page or the site is redirected to a malicious URL. In other cases however the damage might be more vicious, like the addition of a few lines of hidden code that break ranking or a malware uploaded to a folder that is downloaded by users. In this case it might be hard to acknowledge the damage, and perhaps you might notice it when it’s too late: the site has been added to a blacklist whose exit is particularly difficult.
In order to avoid such scenarios you need two different strategies (but interwoven): one is based on plugins, the other on external services. Both monitor the website looking for suspicious file changes, file uploading, non authorized accesses and abnormal traffic coming from geographical areas with a low relevance with your public.
Obviously there must be a proper, quick and complete notification system with email alerts.
BONUS: add you site to Google Search Console, the tool by Google that warns you if an infection or other critical problems are identified.
Sucuri offers the SiteCheck service that checks the security state of your site identifying any anomaly.
The importance of backup
In the IT there is no area where someone might opt for a no-backup policy: the golden rule of performing periodical WordPress backups (and test them) makes no exception.
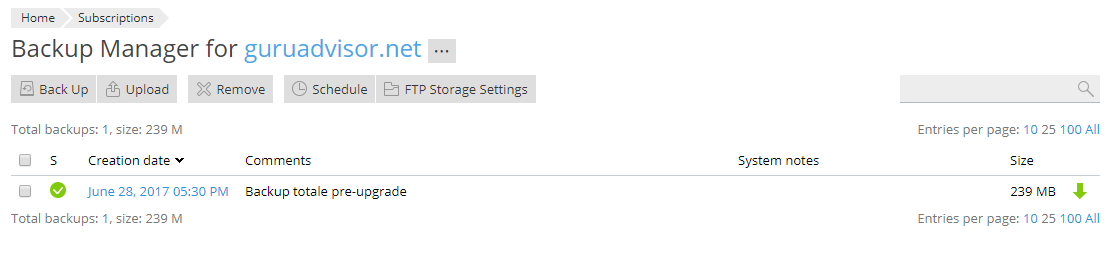
The backup is preferably performed with an automated tool like a dedicated plugin (to be chosen with the aforementioned criteria) or with a function provided by the hosting provider creating an automated backup schedule.
Note that the backup must not reside within the hosting space itself as it’s exposed and if the server experiences a failure, the backup is gone with the server; it must be exported towards another platform (Amazon S3, OneDrive, your own cloud, etc..) or be downloaded locally.
If you perform a manual backup, copy the content of the site root (php, css, js files, images, pdf, audio, video, pictures, etc.) and execute a dump of the MySQL database with phpMyAdmin, with the mysqldump command line command or with the tool provided by your hosting provider.
Backup frequency is calculated according to the update frequency of your site: find the good balance between security and resource usage in the long term.
Finally, backups must be tested: check no files are missing or are corrupted, restore them locally.
The restore of a backup follows the steps required by the solution used to do it, and they might vary from a clean WordPress installation followed by the import of files and database dump to some specific procedures.
BONUS: we have extensively covered the subject of backups with a very interesting article on the 7 golden rules of backups.
Security of the underlying infrastructure
Lastly, some thoughts about the security of the system where WordPress is installed on.
If you rely on a Web Hosting Provider, be sure that the infrastructure is secure, reliable and updated, and that the support is quick and reactive; if you host your site on a VPS, check that everything is secured. Think about adopting a Web Application Firewall (WAF) for your site. A WAF is an application provided as a WordPress plugin or as a service for the underlying structure (VPS or web hosting) that controls the incoming and outgoing traffic blocking it according to specific rules.
Don’t forget to protect the devices you use to administer your site with a proper antivirus solution as well: a key-logger malware might record your access credentials and send them to an hacker, thus frustrating all your efforts made to guarantee a server-side security. But security is never a one-way problem.
Conclusioni
Several studies show how 1 site out of 4 is based on WordPress, and the vast assortment of plugins and themes makes it suitable for any need: just think how WordPress was born as a blogging platform and evolved to be equipped as an eStore.
As a consequence of such diffusion, hackers love it and aim their efforts to it.
By following the best practices of this article you will dramatically reduce the chances of an infection, but bear in mind that there is no way to be 100% safe: so be proactive and adopt a well-designed backup plan that allows you to restore your site in a few time and get back online quickly.