Author
DDoS attacks and botnets
IoT_reaper: a new growing botnet
Netlab researchers identified a new botnet, which was named IoT_reaper.
The botnet is in its first phases and is rapidly growing: it hasn’t launched a single attack up to now but, as the name suggests, hoards vulnerable IoT devices adding them to it network. It is similar to Mirai, although there are some differences: this one only targets vulnerable devices and doesn’t try to hack a password (with a substantial saving in computational resources), it integrates parts of LUA code that allow more sophisticated attacks and its scans are not invasive, so they are hard to identify.
The botnet added more than 20 thousands devices in less than 2 weeks; devices exploited are D-Link, Netgear and Linksys among the others: the full list is in the article linked before. Luckily there are some patches available.
A botnet is scanning the Web for private SSH keys
In a post on its blog, Wordfence warns about a Web scanning activity that looks for private SSH keys left without precautions on web server.
It’s not clear which botnet is responsible for this scan, however Wordfence warns everyone running a site/server and connects with a key-based authentication system.
WordPress 4.8.2 is now available
WordPress release version 4.8.25.
This is a “Security and Maintenance Release” which introduces no new features, instead it fixes some security and performance issues of the most used CMS worldwide.
In particular these 9 problems are fixed, in addition to 6 performance fixes:
- $wpdb->prepare() can create unexpected and unsafe queries leading to potential SQL injection (SQLi). WordPress core is not directly vulnerable to this issue, but we’ve added hardening to prevent plugins and themes from accidentally causing a vulnerability.
- A cross-site scripting (XSS) vulnerability was discovered in the oEmbed discovery.
- A cross-site scripting (XSS) vulnerability was discovered in the visual editor.
- A path traversal vulnerability was discovered in the file unzipping code.
- A cross-site scripting (XSS) vulnerability was discovered in the plugin editor.
An open redirect was discovered on the user and term edit screens. - A path traversal vulnerability was discovered in the customizer.
- A cross-site scripting (XSS) vulnerability was discovered in template names.
- A cross-site scripting (XSS) vulnerability was discovered in the link modal.
The update is available within the dashboard or at this address.
Who wants to preview the upcoming new release, can test WordPress 4.9 beta 3. Obviously it’s only for testing purposes and must not be installed in production environments.
Amazon AWS will open a region in Middle East by 2019
AWS is building a new region in Middle East (Bahrain), whose inauguration is expected by 2019.
It will have 3 Availability Zones (other ones are planned) to allow clients and AWS partners to create virtual instance, manage workloads and store data in Middle East.
Additionally, an “edge location” in the United Arab Emirates is expected to be launched in Q1 2018 which will allow to use the Amazon CloudFront, Amazon Route 53, AWS Shield and AWS WAF services in Middle East.
These two announcements sum to the ones about the opening of two AWS offices in Dubai (UAE) and Manama (Bahrain), testifying the growing attention of Amazon towards this part of the World.
A Cloud Foundry report on containers is available
Cloud Foundry, the open source and multi-cloud Platform-as-a-Service (PaaS) system of the Cloud Foundry Foundation, published a report on container suggestively titled “Hope Versus Reality, One Year Later -- An Update on Containers”.
Amongst the results highlighted by this report, we’d like to point out the growing percentage of companies that adopts container, which ramps from 52% to 67%, both in production (25%) and in evaluation (42%).

OWASP Zed Attack Proxy (ZAP) is an integrated tool dedicated to penetration testing that allows to identify vulnerabilities in Web apps and Websites. It’s an easy and flexible solution that can be used regardless of the proficiency level: it’s suitable for anyone, from a developer at the beginning with pentesting to professionals in the field.
ZAP is composed by two macro-section. The first one is an automated vulnerability scanner that can identify problems and provides a report for developers, sysadmins and security pros with all the details of discovered vulnerabilities in order to fix them.
The second one allows ZAP to work as a proxy and inspect the traffic and all HTTP/S requests and events -- there’s also the interesting capability of modifying them to analyze behaviour that differentiate from the norm or analyze their triggers which can be harmful to the system.
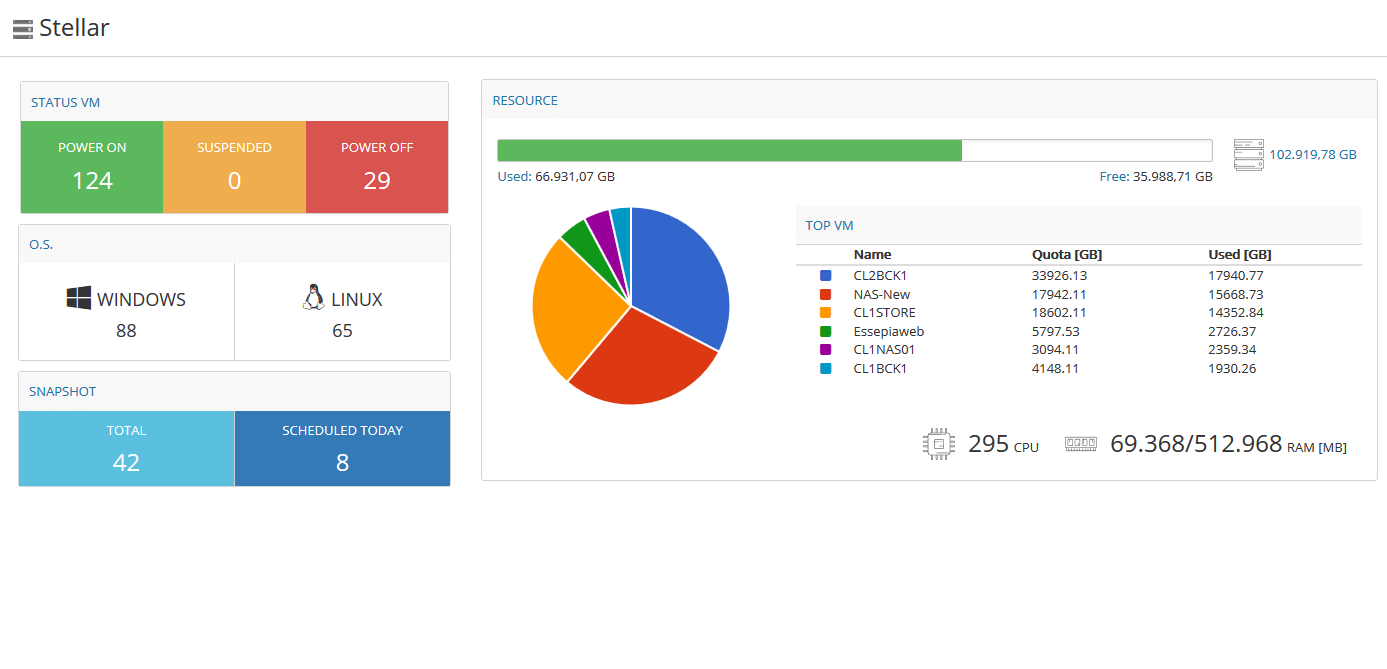
Most companies with IT infrastructures now relies on cloud, public or hybrid cloud systems: Stellar offers Cloud Servers aimed to MSP, EDP Manager, sysadmin, Web Agencies, Software Houses and IT Pros seeking for a reliable and performant cloud system.
Stellar’s cloud servers are best suited to production environments that require, in addition to high performances, a guaranteed service continuity like email and authentication servers, file sharing, remote desktop, database, application software (ERP, CRM, MRP, etc..) and in general all services which rely on virtualization.
A dedicated infrastructure
Stellar relies on two giants of the sector: VMware vSphere and HPE. Servers are grouped into micro-clusters, called Small Cloud Clusters, which are composed by three hosts each. Servers are HP DL360 with double Intel Xeon E5 v3 processor, 192GB of RAM , double 1-GBit 8-port network card and redundant power supply.
Read more Stellar: Cloud Server made in Italy-
BYOD: your devices for your firm
The quick evolution of informatics and technologies, together with the crisis that mined financial mines, has brought to a tendency inversion: users that prefer to work with their own devices as they’re often more advanced and modern than those the companies would provide. Read More -
A switch for datacenters: Quanta LB4M
You don’t always have to invest thousands of euros to build an enterprise-level networking: here’s our test of the Quanta LB4M switch Read More -
Mobile World Congress in Barcelona
GURU advisor will be at the Mobile World Congress in Barcelona from February 22nd to 25th 2016!
MWC is one of the biggest conventions about the worldwide mobile market, we'll be present for the whole event and we'll keep you posted with news and previews from the congress.
Read More
- 1
























